CVE-2019-17507 D-Link DIR-816 Router Authentication Bypass Vulnerability
Introduction
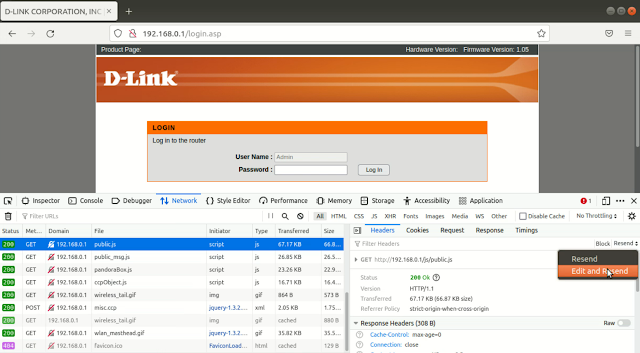
Management pages of D-Link DIR-816 A1 1.06 devices can be accessed without authentication via a client that ignores the 'top.location.href = "/dir_login.asp"' line in a .asp file. Steps to exploit this vulnerability using Burp Suite are given below.
Steps
1. Open the login page of router in Burp Suite browser.
2. Disable HTTP request interception by going to Proxy > Options tab of Burp Suite and uncheck Intercept requests based on following rules checkbox.
3. Enable HTTP server response interception by checking Intercept responses based on the following rules checkbox.
Automation
To automatically delete the line 'top.location.href = "/dir_login.asp;"' from all the responses go to Proxy > Options > Match and Replace section and add a rule as given in figure below.





Comments
Post a Comment